LinkDaddy Cloud Services Press Release: Insights into the most recent Updates
LinkDaddy Cloud Services Press Release: Insights into the most recent Updates
Blog Article
Achieve Service Connection With Secure Cloud Storage Solutions

Benefits of Secure Cloud Storage Space
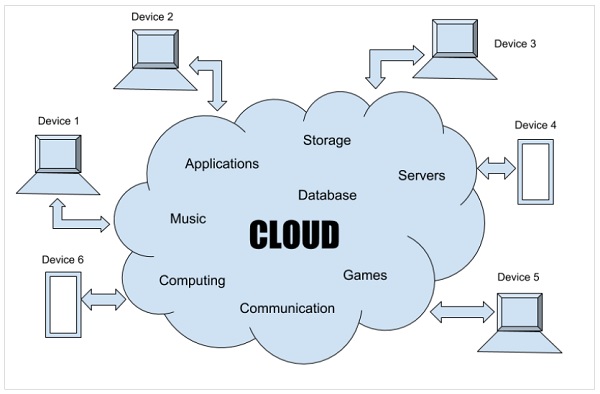
Undoubtedly, protected cloud storage offers companies a plethora of benefits in regards to data security and ease of access. Among the key benefits is boosted safety. By keeping data on credible cloud systems that utilize security and sophisticated safety procedures, businesses can protect their info from unauthorized accessibility or cyber threats. Moreover, protected cloud storage permits smooth scalability, making it possible for organizations to quickly expand their storage room as needed without the headache of physical upgrades. This scalability is particularly advantageous for expanding organizations or those experiencing changing data storage space requirements. In addition, cloud storage space advertises effective collaboration among employee, as it enables real-time access to shared records and documents from anywhere with a net link. This accessibility boosts productivity and streamlines process by removing the constraints of physical storage devices or location-dependent gain access to. Overall, the benefits of safe and secure cloud storage equate into improved information management, raised functional effectiveness, and enhanced protection for companies of all dimensions.
Key Attributes for Company Continuity
By dispersing information across numerous web servers or information facilities, businesses can mitigate the risk of data loss and make sure constant access to their information. Generally, these vital attributes function with each other to create a comprehensive company connection technique that safeguards vital information and operations.
Importance of Information Security
In today's interconnected digital landscape, guarding sensitive details is vital, making the importance of information encryption a basic aspect of keeping data honesty and safety and security. Information file encryption entails encoding details as though just authorized celebrations can access and decipher it. By converting information into a safe layout, file encryption works as a shield against unapproved access, minimizing the danger of data breaches and cyber hazards.
Catastrophe Recovery Strategies
Reliable catastrophe recovery strategies are crucial for services to make sure and reduce potential disturbances continuity when faced with unexpected events. A durable catastrophe recuperation plan involves detailing procedures to recoup data, applications, and IT framework in the event of a calamity. One crucial aspect of an efficient strategy is routine information backups. By saving data in safe and secure cloud storage solutions, businesses can make sure that crucial details is safeguarded and conveniently accessible in instance of a disaster. Checking the calamity recovery strategy regularly is likewise crucial to determine any kind of weaknesses and make required renovations. Additionally, having an assigned group in charge of her response performing the recuperation strategy can minimize and improve the procedure downtime. It is essential to consider various catastrophe circumstances and customize the recuperation strategies to deal with certain threats that business may face. By executing detailed calamity recuperation approaches, organizations can enhance their resilience and safeguard their operations against unforeseen events.
Selecting the Right Company
To make sure smooth organization connection and efficient disaster recuperation, choosing a suitable and reliable company for protected cloud storage space is vital. When selecting a cloud storage solution company, several vital elements must be taken into consideration. Review the supplier's security actions. Ensure they use robust security methods, have rigid access controls, and abide by industry guidelines to safeguard your information. Additionally, examine the provider's data recuperation capabilities. A reliable company need to provide normal backups, redundancy steps, and reliable recovery processes to lessen downtime Discover More Here in case of a catastrophe.
Your service needs might develop over time, so it's essential to pick a company that can accommodate your expanding storage needs and adapt to transforming situations. By carefully examining these elements, you can pick a cloud storage solution provider that lines up with your business's requirements and ensures constant operations in the face of prospective disturbances.
Final Thought
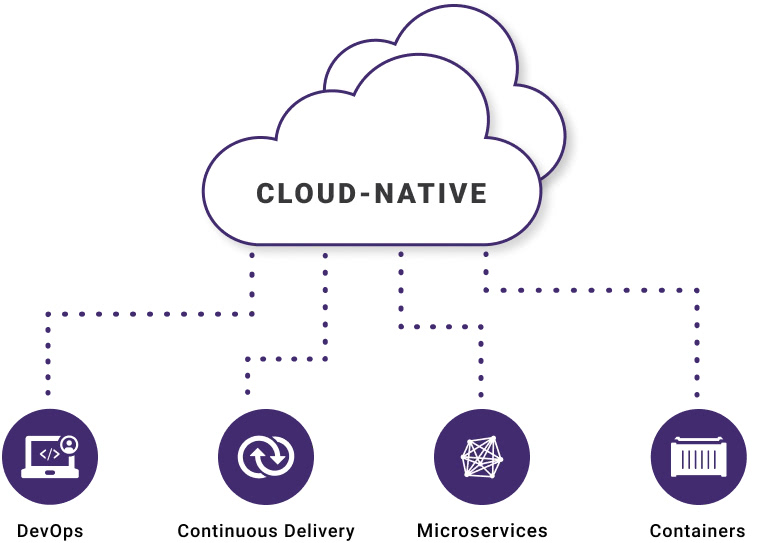
Finally, protected cloud storage space services provide crucial benefits for attaining business continuity, consisting of enhanced safety and security features, seamless scalability, effective collaboration tools, durable information backup systems, and calamity recuperation techniques. Information security plays an essential function in guarding sensitive info, while selecting the appropriate company is vital to ensuring compliance with policies and preserving functional effectiveness. universal cloud Service. Secure cloud storage is an important possession in today's electronic landscape for making certain uninterrupted organization procedures
Data backup mechanisms are essential for safeguarding against data loss due to system failures, cyber-attacks, or human errors. By distributing data across various servers or data facilities, organizations can mitigate the threat of information loss and make certain continual accessibility to their info.In today's interconnected electronic landscape, securing sensitive information is critical, making the importance of data security a basic facet of preserving data integrity and security. By transforming information into a protected format, security acts as a guard against unapproved accessibility, minimizing the danger of data violations and cyber dangers.
Compliance requirements special info and information security policies often mandate the usage of file encryption to protect delicate info, emphasizing its critical duty in contemporary data protection techniques.
Report this page